Prisoners

Here was posted one of the illegal servers created by prisoners
Prison – a place in which Isolate people who are dangerous to society. Here, it is believed, prisoners can be re-educated, persuaded to leave the evil path. The conditions in most prisons are not very good, and people are trying to improve the quality of their lives on their own. For a modern man who is in prison, the situation is further aggravated by a ban on technology. No phones or the usual Internet – nothing.
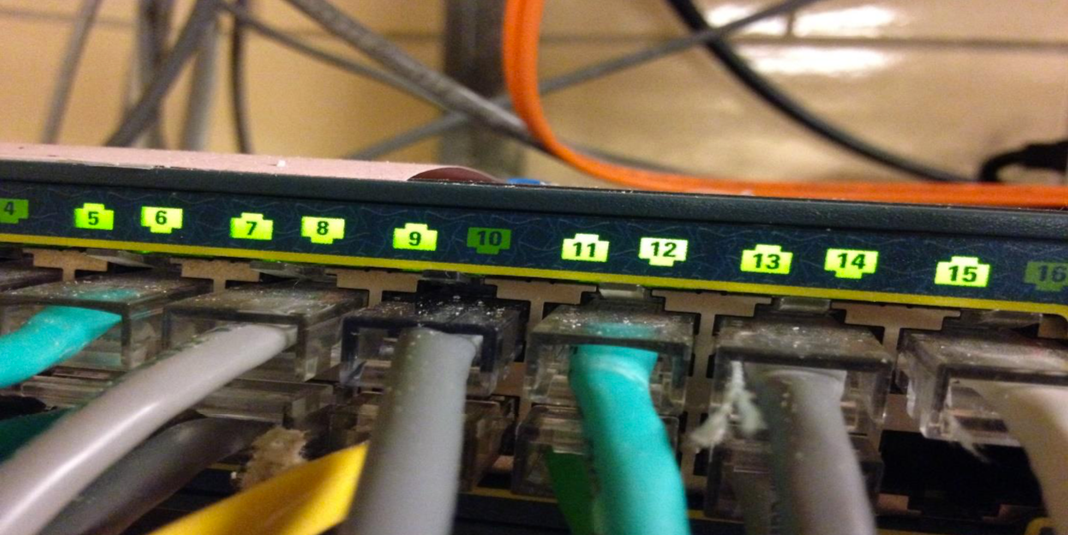
Therefore, criminals (and not only) devise a variety of ways to get all this bypassing ways. Someone carries mobile phones, but someone creates a server and connects it to the prison network to communicate with the outside world. It was this way of improving the conditions of their existence that was chosen by prisoners of one of the American prisons located in Ohio. Re-educated criminals did not even create one, but two working computers, hid them in the ceilings of the ceiling and connected to the prison network.
Hard disks were loaded with pornographic materials and various software, including a proxy server, VPN, VOIP, antivirus, Tor, hacker “gadgets” and a Wireshark packet analyzer. All this became known due to the discovery of a hi-tech cache by the prison staff.
All the elements of the created computers were obtained from acquaintances and friends who somehow managed to transfer details with parcels. Found the work of prison hackers by sheer accident. Those began to download a large amount of data that was noticed by the administrator. In this prison there is a certain limit on traffic, which from a certain moment began to be exceeded for no apparent reason. Plus, once the administrator of the prison network received a system warning about the connected device.
The prisoners managed to hide their actions for about four months. After that, the jailers began searches and checks throughout the prison, as it became clear that something unplanned was happening, and additional terminals appeared in the prison network. Computers were found in the ceiling of the toilet ceiling, here the supervision of prisoners is not as strict as in the rest of the prison. In general, it was not too difficult to find computers, since all that was required to do was to trace the “illegal” systems through a twisted pair. This was done.
The authorities were able to even understand where the computer parts came from – the unincorporated supplier was the aircraft manufacturing company and the management of the region’s schools.
A thorough analysis of the media showed that the hard drives were simply clogged with pornographic materials as well as hacking software that provided prisoners with the ability to hack blocked sections of the prison network, gaining access to the enclosed premises. A large amount of information has been found on how to make narcotics, explosives and other materials and things outside the laboratory. The data of stolen credit cards with which prisoners paid access to various network resources and ordered goods were also found.
Of course, these computers were used to communicate with the outside world. Thus, the authorities found the correspondence of some prisoners with relatives and friends. “I wanted to write yesterday, but I could not go online,” said a message from one of the prisoners who was communicating with his mother.
Five people were responsible for the incident, who were transferred to other prisons.
The report of the agency conducting the investigation reads: “The prisoners took the case and some parts of the computers that were supposed to be dismantled for spare parts, installed hard drives, a network card, computers were carried On the prison a few hundred meters, and they managed to carry through the point of inspection, the institution’s employees did not check the prisoners, they got access to the elevator, went up to the third floor and placed computers in the ceilings of the ceiling. ” In addition, the prisoners were able to connect their systems to the electrical network and the computer network of the prison without any problems.
Chief Inspector Randall Meyer said that he was very surprised by this situation. “I was surprised not only that prisoners could connect to a computer network, but also that they collected computers. They managed to carry systems several hundred meters without checking by the prison staff, and there were several points of inspection, after which they entered the administrative part of the prison, “he said.
Now officials are going to fix some gaps in the state prison security system, which made it possible to create an illegal prison computer network with their own servers. Employees of agencies responsible for the functioning of prisons say they are going to do everything to prevent the situation from happening again. But who knows, to speak is one thing, and to achieve is quite another.